GeoServer Blog
GeoServer 2.26.0 Release
GeoServer 2.26.0 release is now available with downloads (bin, war, windows), along with docs and extensions.
This is a stable release of GeoServer recommended for production use. GeoServer 2.26.0 is made in conjunction with GeoTools 32.0, GeoWebCache 1.26.0, ImageIO-EXT 1.4.13, and JAI-EXT 1.1.27.
Thanks to Peter Smythe (AfriGIS) and Jody Garnett (GeoCat) for making this release and everyone who has helped out during this release cycle. Special thanks Andrea for helping with release announcement, and Torben for troubleshooting the build server and docker environment for this release.
Nightly build testing
This release cycle we asked our new user forum to test a nightly build, as we did not have capacity to make a release candidate.
Thanks to Daniel Calliess for responding during our public testing cycle. Daniel noted that he had to add /geoserver/webresources to his proxy for the OpenLayers preview to function. This change is due to an ongoing effort to move all CSS and JS to external resources allowing Content Security Policy headers to be introduced.
Security Considerations
This release addresses security vulnerabilities and is a recommended upgrade for production systems.
- CVE-2024-34711 Improper ENTITY_RESOLUTION_ALLOWLIST URI validation in XML Processing (SSRF) (High)
- CVE-2024-35230: Welcome and About GeoServer pages communicate version and revision information (Moderate)
- CVE-2024-40625 Coverage REST API Server Side Request Forgery (Moderate)
- CVE-2025-21621 Reflected Cross-Site Scripting (XSS) vulnerability in WMS GetFeatureInfo HTML format (Moderate)
See project security policy for more information on how security vulnerabilities are managed.
- GEOS-11400 About Page Layout and display of build information
Java 17 Support
The binary distribution and the Windows installer now work with Java 17.
When using the war distribution with Tomcat and Java 17 double check the Server status page. If the Java Rendering Engine is listed as “Unknown”, double check the Running in Java 17 production considerations.

Thanks to Andrea Aime and everyone who worked on testing this in different environments.
- GEOS-11467 Update Marlin, make the bin package compatible with Java 17
Docker Updates
The base image tomcat:9.0.95-jdk17-temurin-jammy is now used - providing the latest Tomcat 9 and Java 17. The docker crew changed from using ubuntu:22.04 with our own Tomcat install script earlier in the year.
To try out GeoServer 2.26.0 with docker:
docker pull docker.osgeo.org/geoserver:2.26.0
docker run -it -p8080:8080 docker.osgeo.org/geoserver:2.26.0
Thanks to Nils Bühner (terrestris) and everyone who has contributed to the Docker build.
Search improvement
A small but fun change for the layer preview - it is now easier to find just the layer you are looking for using quotes to isolate an individual word.

Thanks to Alessandro Ricchiuti for this work.
- GEOS-11351 Exact term search in the pages’ filters
Extensive MapML Improvements
Thanks to Natural Resources Canada for sponsoring an extensive set improvements for the MapML extension.

This update was carried out by a group of GeoSolutions devs, Andrea Aime, Daniele Romagnoli and Joseph Miller.
- GEOS-11322 MapML WMS Vector Representation include query filter
- GEOS-11324 MapML WMS Vector Representation Style Classes
- GEOS-11337 Support feature tiles in MapML
- GEOS-11349 MapML Use WMS Resource Consumption Limit to specify max image size
- GEOS-11461 Enable MapML Viewer output for WFS getFeature.
- GEOS-11486 Adding custom dimensions to MapML
- GEOS-11528 Update MapML viewer to latest release 0.14.0
- GEOS-11471 Remove Sharding configuration support from MapML
Demo Requests page rewritten
The Demo Request page has been rewritten to use JavaScript to issue POST examples. This provides a much better user experience:
- Show Result lists the response headers to be viewed along side the returned result (with an option for XML pretty printing).
- Show Result in a New Page is available to allow your browser to display the result.
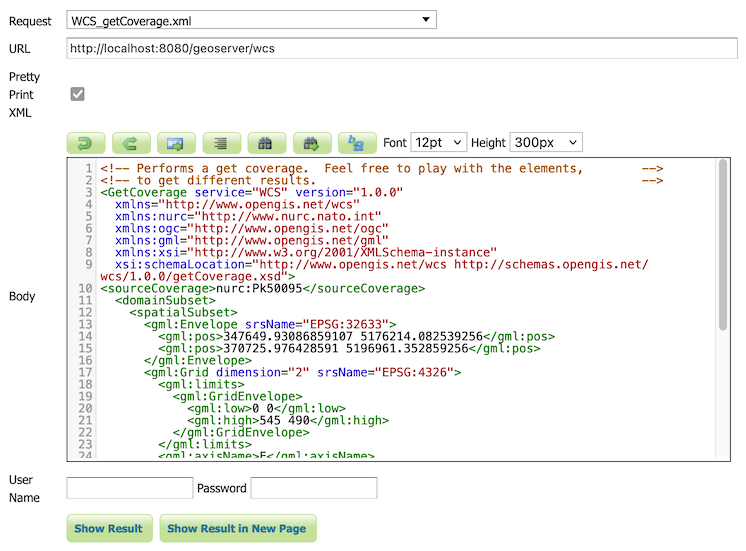
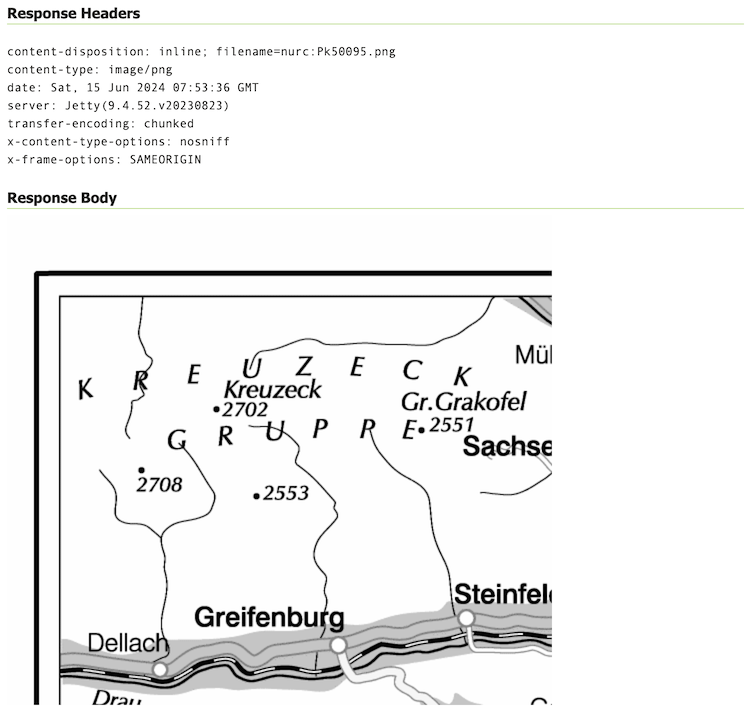
The WCS Request Builder and WPS Request Builder demos now have the option to show their results in Demo Requests page. Combined these changes replace the previous practice of using an iframe popup, and have allowed the TestWfsPost servlet to be removed.
For more information please see the Demo requests in the User Guide.
Thanks to David Blasby (GeoCat) for these improvements, made on behalf of the GeoCat Live project.
- GEOS-11390 Replace TestWfsPost with Javascript Demo Page
JTS 1.20.0 Update
We are overjoyed to update to the latest JTS 1.20.0 release which includes a new implementation of spatial relationships.
Use -Djts.relate=ng to try out the new implementation (replacing RelateOp with theReleateNG next generation implementation). Let us know how it goes, a future update will make this setting the default and expand the approach to “prepaired geometry” bulk operations used for WFS Queries.
Thanks to Martin Davis (CrunchyDB) for the JTS improvements, and Jody Garnett (GeoCat) for the release and GeoServer update.
- GEOS-11532 Update to JTS 1.20.0
Raster Attribute Table Extension
A new extension is available that takes advantage of the GDAL Raster Attribute Table (RAT). This data structure provides a way to associate attribute information for individual pixel values within the raster. This provides a table that links each cell value in the raster to one or more attributes on the fly.
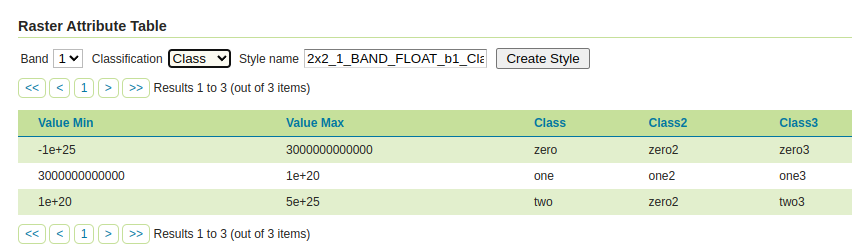
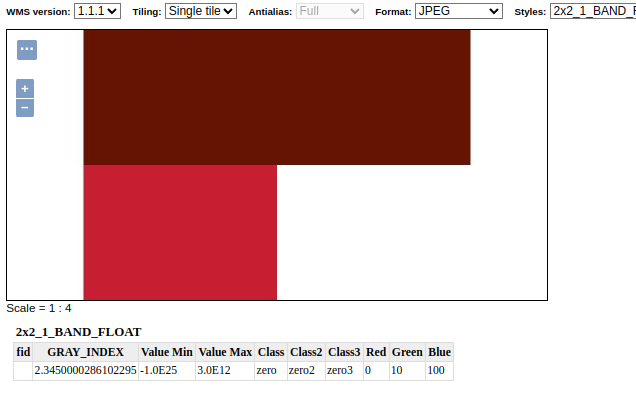
Thanks to Andrea Aime (GeoSolutions) for the development and NOAA for sponsoring this new capability. Please see the user guide Raster Attribute Table support for more information.
- GEOS-11376 Graduate Raster Attribute Table to extension
GeoCSS improvements
GeoCSS can now perform scale dependent rendering by the zoom level, assuming web mercator by default, but allowing the configuration of a different gridset as well. It’s also possible to create multi-layer styles and use them as style groups.
@mode 'Flat';
@TileMatrixSet 'WorldCRS84Quad'
tiger:poly_landmarks {
/* @title parks and green spaces */
[CFCC in ('D82', 'D32', 'D84', 'D85')] {
fill: #B4DFB4;
stroke: #88B588;
};
…
}
tiger:tiger_roads [@z > 12] {
stroke: #666666, #FFFFFF;
stroke-width: 6, 4;
z-index: 1, 2;
…
}
…
Thanks to Andrea Aime (GeoSolutions) for this work, performed in preparation for the FOSS4G-NA 2024 vector tiles workshop.
- GEOS-11495 Support multi-layer output in CSS
- GEOS-11515 Add support for zoom level rule filtering in CSS
- GEOS-11414 Adding css-uniqueRoleName
Geostationary satellite AUTO code
AUTO:97004 has been introduced as a new vendor extension to WMS AUTO codes. It implements the geostastionary satellite project and allows to change the central meridian as part of the GetMap request.

Thanks to Andrea Aime (GeoSolutions) for this work, and Eumetsat for sponsoring it.
labelPoint function improved
The labelPoint function has been improved with more precise calculation of the polygon label points, and not requiring to specify a tolerance any longer. This helps get better maps, especially with tiling enabled (fixed labelling point no matter which tile is requested):
<sld:TextSymbolizer>
<sld:Geometry>
<ogc:Function name="labelPoint">
<ogc:PropertyName>the_geom</ogc:PropertyName>
</ogc:Function>
</sld:Geometry>
</sld:TextSymbolizer>


Thanks to Andrea Aime (GeoSolutions) for this work, performed in preparation for the FOSS4G-NA 2024 vector tiles workshop.
Improved vector tiles generation
A few new vendor options have been added in GeoServer, that control how vector tiles are built, with the objective of producing smaller, faster, more useful vector tiles.
vt-attributes: comma separated list of attributes included in the vector tilevt-labels: when true, generates a sidecar-labellayer for polygons, with the label point of the polygon (vector tile clients generally cannot produce a good label placement otherewise)vt-label-attributes:: attributes included in the label point layervt-coalesce: if true, takes all features in the tile sharing the same attribute values, and coalesces their geometries into a single multi-geometry.
Here is an example style using the above vendor options, in GeoCSS:
@mode "Flat";
tiger:poly_landmarks {
fill: gray;
vt-attributes: 'CFCC,LANAME';
vt-labels: true;
}
tiger:tiger_roads [@z > 11] {
stroke: black;
vt-attributes: 'NAME';
vt-coalesce: true;
}
tiger:poi [@z > 12] {
mark: symbol(square);
}
The GWC layer preview has also been improved to show the vector tile feature attributes on hover:

Thanks to Andrea Aime (GeoSolutions) for this work, performed in preparation for the FOSS4G-NA 2024 vector tiles workshop.
GeoPackage QGIS Compatibility Improvements
A number of issues affecting interoperability with QGIS have been addressed:
GeoPackage extension output could contain field types that are not supported by GDAL. It turns out the GeoPackage export was picking up some of the file type information intended for PostGIS resulting output that could not be read by other programs such as QGIS.
We were also able to fix up the TIMESTAMP information representation as DATETIME, making the file format timezone agnostic as intended.

Thanks to David Blasby (GeoCat) for these fixes made on behalf of Zeeland and South Holland.
- GEOS-11416 GeoPackage output contains invalid field types when exporting content from PostGIS
New image mosaic merge behaviors, MIN and MAX
These two new image mosaic merge modes activate when multiple images overlap with each other, choosing respectively the minimum and maximum value amongst the super-imposed pixels.

Thanks to Andrea Aime for the work, and the US National Research Laboratory for sponsoring it.
Release notes
New Feature:
- GEOS-11322 MapML WMS Vector Representation include query filter
- GEOS-11324 MapML WMS Vector Representation Style Classes
- GEOS-11352 REST service for URL checks
- GEOS-11376 Graduate Raster Attribute Table to extension
- GEOS-11390 Replace TestWfsPost with Javascript Demo Page
- GEOS-11414 Adding css-uniqueRoleName
Improvement:
- GEOS-11271 Upgrade spring-security to 5.8
- GEOS-11325 Add properties to set additional security headers
- GEOS-11337 Support feature tiles in MapML
- GEOS-11338 CapabilityUtil SearchMinMaxScaleDenominator should include support for multiple NamedLayers
- GEOS-11349 MapML Use WMS Resource Consumption Limit to specify max image size
- GEOS-11351 Exact term search in the pages’ filters
-
GEOS-11369 Additional authentication options for cascaded WMS WMTS data stores - GEOS-11370 Refactor inline JavaScript in the TestWfsPost Page
- GEOS-11371 Refactor inline JavaScript in the GetMap OpenLayers format
- GEOS-11379 Refactor inline JavaScript in the OGC API modules
- GEOS-11400 About Page Layout and display of build information
- GEOS-11401 Introduce environmental variables for Module Status page
- GEOS-11427 metadata: “fix all” to support changing config repeatable field
- GEOS-11443 REST API does not take effect immediately due to 10 minute authentication cache
- GEOS-11461 Enable MapML Viewer output for WFS getFeature.
- GEOS-11467 Update Marlin, make the bin package compatible with Java 17
- GEOS-11477 Add a max and a min merge mode for image mosaics
- GEOS-11486 Adding custom dimensions to MapML
- GEOS-11488 Double-Click-to-Copy featurecaption variable reference
- GEOS-11495 Support multi-layer output in CSS
- GEOS-11502 Permit resize on user/group/role palette textbox to allow for extra long role names
- GEOS-11503 Update mongo schemaless DWITHIN to support non-point geometry
- GEOS-11515 Add support for zoom level rule filtering in CSS
- GEOS-11526 GeoFence: slow GeoServer response when there are many roles and layergroups
- GEOS-11527 Add new vector tiles generation options in style body: vt-attributes, vt-coalesce, vt-labels, vt-label-attributes
- GEOS-11528 Update MapML viewer to latest release 0.14.0
- GEOS-11531 When coalescing linestrings in vector tiles output, fuse them to create a single long line
Bug:
- GEOS-7183 Demo request/wcs/wps pages incompatible with HTTPS/PKI
- GEOS-11202 CAS extension doesn’t use global “proxy base URL” setting for service ticket
- GEOS-11266 csw-iso: missing fields in summary response
- GEOS-11314 Error in IconService when style has multiple FeatureTypeStyle
- GEOS-11385 Demo Requests functionality does not honour ENV variable PROXY_BASE_URL
- GEOS-11416 GeoPackage output contains invalid field types when exporting content from PostGIS
- GEOS-11422 MapML License Metadata Stored With Incorrect Keys
- GEOS-11430 CiteComplianceHack not correctly parsing the context
- GEOS-11446 [INSPIRE] Incorrect behavior for unsupported languages
- GEOS-11462 500 error thrown when double adding a user to a group via REST with JDBC user/group services
- GEOS-11484 DirectRasterRenderer is not respecting advancedProjectionHandling and continuosMapWrapping format_options
- GEOS-11530 Adding or removing a grid subset in the layer caching tab, causes the grid dropdown to get duplicated
Task:
- GEOS-11341 Upgrade NetCDF to 5.3.3
- GEOS-11360 Upgrade Apache POI from 4.1.1 to 5.2.5
- GEOS-11362 Upgrade Spring libs from 5.3.32 to 5.3.33
- GEOS-11374 Upgrade Spring version from 5.3.33 to 5.3.34
- GEOS-11375 GSIP 224 - Individual contributor clarification
- GEOS-11393 Upgrade commons-io from 2.12.0 to 2.16.1
- GEOS-11395 Upgrade guava from 32.0.0 to 33.2.0
- GEOS-11397 App-Schema Includes fix Integration Tests
- GEOS-11402 Upgrade PostgreSQL driver from 42.7.2 to 42.7.3
- GEOS-11403 Upgrade commons-text from 1.10.0 to 1.12.0
- GEOS-11404 Upgrade commons-codec from 1.15 to 1.17.0
- GEOS-11407 Upgrade jackson from 2.15.2 to 2.17.1
- GEOS-11464 Update Jackson 2 libs from 2.17.1 to 2.17.2
- GEOS-11470 Upgrade the version of Mongo driver for schemaless plugin from 4.0.6 to 4.11.2
- GEOS-11471 Remove Sharding configuration support from MapML
- GEOS-11472 Upgrade freemarker from 2.3.31 to 2.3.33
- GEOS-11473 Upgrade guava from 33.2.0 to 33.2.1
- GEOS-11475 Upgrade commons-codec from 1.17.0 to 1.17.1
- GEOS-11478 Upgrade commons-lang3 from 3.14.0 to 3.15.0
- GEOS-11479 Upgrade junit from 4.13.1 to 4.13.2
- GEOS-11480 Update map fish-print-lib 2.3.1
- GEOS-11506 Upgrade Spring version from 5.3.37 to 5.3.39 and Spring security from 5.8.13 to 5.8.14
- GEOS-11508 Update OSHI from 6.4.10 to 6.6.3
- GEOS-11512 Upgrade jasypt from 1.9.2 to 1.9.3
- GEOS-11532 Update to JTS 1.20.0
- GEOS-11533 Update org.apache.commons.vfs2 to 2.9.0
- GEOS-11544 Upgrade to ImageIO-EXT 1.4.13
- GEOS-11545 Update to JAI-EXT 1.1.27
For the complete list see 2.26.0 release notes.
Community Updates
Community modules are shared as source code to encourage collaboration. If a topic being explored is of interest to you, please contact the module developer to offer assistance.
Community module development:
- GEOS-10690 Task manager plugin is missing dependencies
- GEOS-10824 gs-flatgeobuf extension can clash with “directory of shapefiles” datastores
- GEOS-11331 OAuth2 can throw a “ java.lang.RuntimeException: Never should reach this point”
- GEOS-11358 Feature-Autopopulate Update operation does not apply the Update Element filter
- GEOS-11381 Error in OIDC plugin in combination with RoleService
- GEOS-11412 Remove reference to JDOM from JMS Cluster (as JDOM is no longer in use)
- GEOS-11466 move reusable elements of the graticule plugin to GeoTools
- GEOS-11469 Datadir catalog loader does not decrypt HTTPStoreInfo passwords
- GEOS-11518 DGGS JDBC store SQL encoder should not force the timezone to CET
- GEOS-11519 Make DGGS rHealPix tests run again
- GEOS-11521 Expose a JNDI variant of the DGGS Clickhouse datastore
- GEOS-11541 STAC search endpoint sortby query not working with POST
OGC APIs feeling “at home”
OGC API modules now nicely slot into the home page in the corresponding functional section, e.g., since both provide raw vector data, both OGC API Features and WFS show up in the same area:

Thanks to David Blasby (GeoCat) for this work.
- GEOS-11445 OGCAPI ServiceDescriptors
Data directory loader
The “Data Directory loader”, by Gabriel Roldan (Camptocamp), is a replacement data directory loader, reading the XML configuration files at startup. It has been optimized to achieve better parallelism and be more efficient over network file systems.
It can be found amongst the nightly builds, it’s a simple drop in replacement, just unzip the plugin in WEB-INF/lib and restart. Let us know how it works for you.
WFS HTML Freemarker output
The WFS HTML Freemaker output format is a community module generating HTML in response to GetFeature, using the GetFeatureInfo Freemarker templates.
Thanks to Alessio Fabiani (GeoSolutions) for starting this activity.
Graticule module
The graticules module is the combination of a data store and a rendering transformation allowing to generate graticules at multiple resolutions, and optionally placing the graticule labels at the map borders.

Thanks to Ian Turton for working on this activity. Ian needs a few more people to try this out before it can be included in our GeoServer roadmap.
Developer Updates
GeoServer team has identified quite the challenges for GeoServer 2024 Roadmap Plannings.
Wicket Progress
After initial testing of 2.26-M0 milestone release we held off including Wicket 9 until after the 2.26.0 release. Thanks to Peter Smythe and Jody Garnett for testing.
Thanks to Brad Hards who started this work in November 2023, and David Blasby who helped bring this up to a state it could be tested ahead of the 2.26.0 release.
Spring Security 5.8
Thanks to Andreas Watermeyer (ITS Digital Solutions) completed this important update.
This is the last stopping place before Spring Security 6, and the last chance to work with the OAuth2 community modules.
- GEOS-11271 Upgrade spring-security to 5.8
About GeoServer 2.26 Series
Additional information on GeoServer 2.26 series:
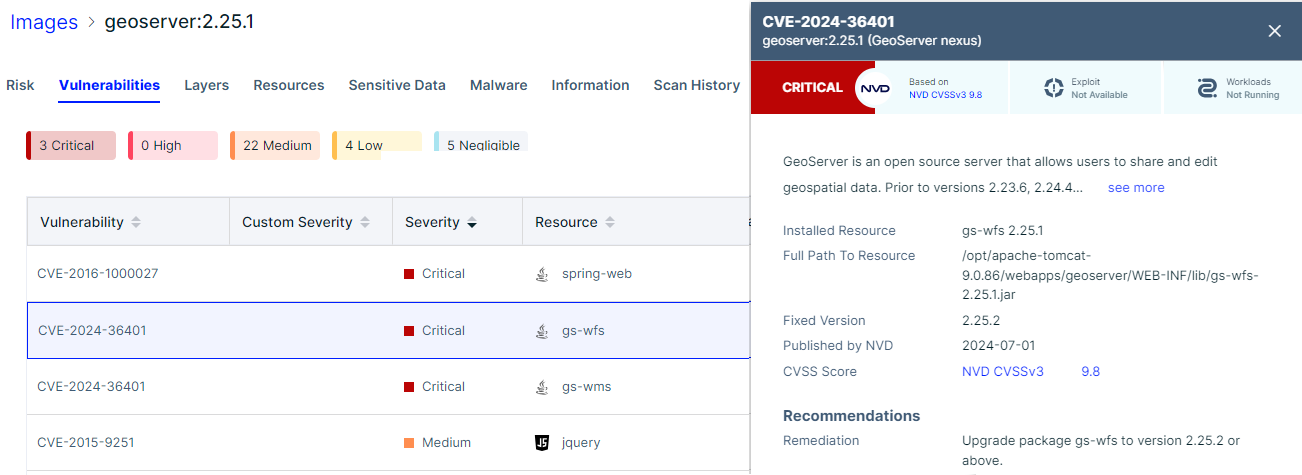
CVE-2024-36401 Remote Code Execution (RCE) vulnerability in evaluating property name expressions
The GeoServer community has been under considerable strain responding to CVE-2024-36401. This vulnerability stems from GeoTools library CVE-2024-36404.
This vulnerability, in the handling of XPath expressions, affords a “remote code execution” attack that is under active exploit. A remote code execution (RCE) attack allows an attacker to run malicious code on your computer or network.
For more information:
- GeoServer 2.25.2 Release (Jun 18, 2024)
- GeoServer 2.24.4 Release (Jun 18, 2024)
- GeoServer 2.22.6 Release (Mar 17, 2025)
- CVE-2024-36401 (July 1, 2024)
- CISA Warns of Actively Exploited RCE Flaw in GeoServer GeoTools Software (The Hacker News, July 18, 2024)
- GeoServer Vulnerability Targeted by Hackers to Deliver Backdoors and Botnet Malware (The Hacker News, September 6, 2024)
Q: Why have I been directed to this post?
You are responsible for running a GeoServer instance that has not been updated.
-
CVE-2024-36401 provides mitigation instructions which you should perform immediately.
Please stop reading and do this now.
-
Update your instance: Upgrading existing versions (User Guide)
The instructions include notes on upgrading specific versions. Please read carefully to see if any manual changes are required.
Q: Do I have to update or is a patch available?
With such a serious issue several service providers have stepped forward to make fixes available for prior releases.
Full release:
- GeoServer 2.23.6 Release (GeoCat)
Patch provided with CVE-2024-36401 report:
- GeoServer 2.25.1 (GeoSolutions)
- GeoServer 2.24.3 (GeoSolutions)
- GeoServer 2.24.2 (GeoSolutions)
- GeoServer 2.23.2 (GeoSolutions)
- GeoServer 2.22.2 (GeoSolutions)
- GeoServer 2.21.5 (GeoSolutions)
- GeoServer 2.21.4 (GeoSolutions)
- GeoServer 2.20.7 (GeoSolutions)
- GeoServer 2.20.4 (GeoSolutions)
- GeoServer 2.19.2 (GeoSolutions)
- GeoServer 2.18.0 (GeoSolutions)
Free software is a participation sport - to create a patch for a prior release volunteer with community development.
Q: How often should I upgrade GeoServer?
GeoServer operates with a time boxed release cycle, maintaining “stable” and “maintenance” releases, over the course of a year.
-
Upgrade GeoServer twice a year as new stable releases are made.
-
Once the release you are using has entered “maintenance” it is a good idea to upgrade (before the release is no longer supported).
-
GeoServer security policy provides one year of support. You may also contact our service providers for extended support beyond this timeframe.
Q: Notification of security vulnerabilities?
Stay up to date:
-
Please monitor release announcements for the heading “Security Considerations”.
Security Considerations
This release addresses security vulnerabilities and is considered an essential upgrade for production systems.
- CVE-2024-36401 Critical
You can review the release announcement, and in this case with a “Critical” vulnerability decide to update.
-
When everyone has had an opportunity to update the details of the vulnerability are announced.
Security Considerations
This release addresses security vulnerabilities and is considered an essential upgrade for production systems.
- CVE-2024-36401 Remote Code Execution (RCE) vulnerability in evaluating property name expression (Critical)
-
As GeoServer has now adopted use CVEs for publication you may also have success with vulnerability scanning tools.
These tools function when the vulnerability is published, and do not provide any advance notice.
Q: Notification of security reports?
As security reports contain sensitive information they are only shared with representatives of the geoserver-security email list.
Participation in geoserver-security, like commit access, is volunteer based and reflects trust.
Please review GeoServer Security Policy if you are in a position to help out.
GeoServer 3 Call for Crowdfunding
GeoServer is at a critical turning point and it needs your help to continue its journey as the leading free and open-source platform for geospatial data. With GeoServer 3 we are transforming the way you interact with geospatial data—making it faster, more intuitive, and more secure.
This major upgrade, led by Camptocamp, GeoSolutions, and GeoCat, will deliver:
-
Future-Proof Performance: A modernized core for compatibility with the latest data management and deployment technologies.
-
Enhanced Image Processing: Faster, smoother handling of spatial imagery and larger datasets.
-
Improved Security and Compliance: Meet regulatory standards and protect your data with the latest security enhancements.
-
Streamlined User Experience: Easier navigation, integrating new services, and empowering users at all levels.
The scope of this work is beyond routine updates or maintenance since the transition to GeoServer 3 requires extensive redevelopment of core systems as well as implementing modern security practices and also thorough testing and validation across all GeoServer extensions.
The consortium members - Camptocamp, GeoSolutions, and GeoCat- have a long-standing history of supporting and contributing to GeoServer and are fully committed to the success of this migration. However, this is a major effort that cannot be completed without community support.
By supporting this crowdfunding campaign, you are investing in the future of GeoServer and helping to sustain the innovative, open-source geospatial community.
Why GeoServer 3
As the digital landscape evolves, staying up-to-date with the latest technology is no longer optional — it’s essential. GeoServer 3 is being developed to address crucial challenges and ensure that GeoServer remains a reliable and secure platform for the future. Several key factors make this upgrade critical right now:
-
Regulatory Compliance: New regulations, including the CISA known exploited vulnerabilities list, demand that systems be fully patched to ensure operational readiness. Without the latest updates, GeoServer risks falling short of these standards, which is why migrating to Spring 6 is essential.
-
End of Support for Spring 5: By January 2025, Spring 5 will no longer receive security updates, leaving systems vulnerable. As GeoServer operates as middleware between web services and essential data layers, this upgrade to Spring 6 is crucial to maintaining secure connections and protecting data from potential breaches.
-
Security Enhancements: Upgrading to Spring 6 enables OAuth2 protocols for secure authentication, especially critical for large-scale or enterprise-level use. These advancements will help organizations meet evolving security requirements and protect sensitive geospatial data.
-
Switching to JDK 17: This upgrade also marks GeoServer’s transition to JDK 17, which brings improvements in performance, security, and long-term support. Keeping GeoServer aligned with the latest Java versions ensures compatibility with modern deployment technologies Tomcat 10 and Jakarta and future-proofs the platform.
-
Improved Image Processing: GeoServer 3 will replace the outdated Java Advanced Imaging (JAI) library with the more modern and flexible ImageN toolkit. This switch will significantly enhance image processing capabilities, enabling faster handling of large spatial datasets and improving Java compatibility.
-
Future-Proof Technology Stack: With the migration to Spring 6 and the shift to JDK 17, GeoServer 3 ensures long-term viability. Addressing the entire GeoServer stack, including enterprise components GeoFence and Cloud Native GeoServer, allows organizations to seamlessly adopt modern infrastructure and deployment models without compromising performance or security.
With this work, GeoServer is moving into a more secure, high-performing future—ready to tackle the evolving needs of the geospatial community. For more information on the work to be performed and its phases, please visit this document.
Crowdfunding structure
The crowdfunding will be structured in two phases to ensure success:
-
Commitment Phase: Sponsors and community members will pledge their financial support during this phase, but no funds will be collected. The goal is to reach a predefined target that covers the full scope of work necessary for the migration.
-
Funding Activation: Once the target is reached, the crowdfunding will be activated, and sponsors will be invoiced for their pledged amounts. This ensures there is enough financial backing to complete the migration without risking underfunding.
This structured approach ensures that GeoServer 3 is fully funded before any work begins, preventing the risk of an incomplete migration. This guarantees that the project will have the necessary resources to be completed in its entirety.
This structure forms a multi-party agreement:
-
Consortium: Three companies are forming a consortium (Camptocamp, GeoSolutions, and GeoCat) providing expertise, a proven track record, and capacity. These companies are also taking on responsibility for project management, estimating, and importantly risk.
-
Supporters: We are seeking organisations to pledge their support via funding during the commitment phase. No funds will be collected until we reach the target established below for the full scope of work necessary.
-
Community: We ask that our community step forward to match the contributions above with both financial contributions and in-kind development and testing.
Crowdfunding target
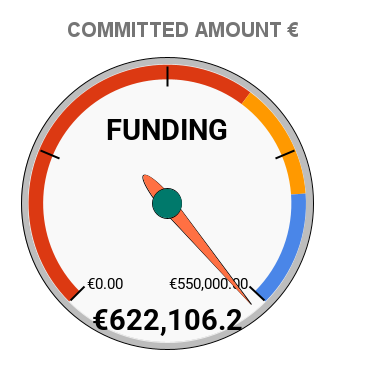
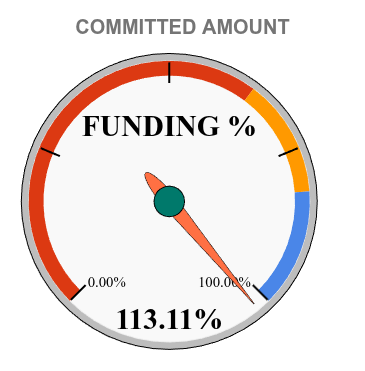
The financial target is ambitious, 550,000.00 €. CamptoCamp, GeoCat and GeoSolutions have generously stepped up and will provide 50,000.00€ each, which means the current funding goal starts at 400,000.00 €. Here below you will find the live updated situation as far as committed funding is concerned.
How to participate
If you are ready to support GeoServer 3, please, fill this online form or contact us at gs3-funding@googlegroups.com to express your interest and pledge your support.
Together, we can secure the future of GeoServer for years to come.

Using Value Comparison Operators in GeoServer Filters
GeoSpatial Techno is a startup focused on geospatial information that is providing e-learning courses to enhance the knowledge of geospatial information users, students, and other startups. The main approach of this startup is providing quality, valid specialized training in the field of geospatial information.
( YouTube | LinkedIn | Facebook | X )
Value Comparison Operators in GeoServer Filters
In this session, we want to talk about the various types of filters, with a particular focus on “Value comparison operators in GeoServer” comprehensively. If you want to access the complete tutorial, click on the link.
Introduction
Filtering allows the selection of features that satisfy a specific set of conditions. Filters can be used in several contexts in GeoServer:
- In WMS requests, select which features should be displayed on a map
- In WFS requests, specify the features to be returned
- In SLD documents, apply different symbolizations to features on a thematic map
Note. This video was recorded on GeoServer 2.22.4, which is not the most up-to-date version. We encourage all users to use the stable series, currently 2.28.x. To ensure you have the latest release, please visit this link and avoid using older versions of GeoServer.
Comparison operators
In GeoServer, the Web Feature Service (WFS) filtering utilizes a set of comparison operators to facilitate the querying of geospatial features. These operators allow users to create precise filters based on attribute values, enabling robust spatial queries. The main comparison operators available include: Binary comparison operators and Value comparison operators.
The value comparison operators are:
- PropertyIsLike
- PropertyIsNull
- PropertyIsBetween
PropertyIsLike
The PropertyIsLike operator is used to compare a string property value with a text pattern. It includes the
These characters are defined by the attributes of the
- WildCard: It specifies the pattern character that matches any sequence of zero or more string characters
- SingleChar: It specifies the pattern character that matches any single string character
- EscapeChar: It specifies the escape character which can be used to escape the pattern character
Geoserver supports the PropertyIsLike operator within filter expressions for querying spatial data. Here are some examples of how you can use this filter in an XML request to filter the States layer by the State_Name attribute:
- Navigate to the Demos page, then select Demo requests.
- From the Request section, select the WFS_getFeature1.0.xml request.
- The address will be filled in automatically, in the URL section.
Use the following block codes to replace line 26:
<PropertyIsLike wildCard="*" singleChar="_" escapeChar="\">
<PropertyName>STATE_NAME</PropertyName>
<Literal>North*</Literal>
</PropertyIsLike>
- Now, we will explain some elements:
- The first fifteen lines include explanations in the form of comments.
- Line 16 describes the XML version and the GetFeature operation of the WFS service being used.
- Line 17 specifies the default output format for the WFS service as “gml2.” Additionally, GeoServer supports several other commonly used formats such as “gml3, shapefile, geojson, and csv.”
- Lines 18 to 23 define the start of the XML request and declare the namespaces used in the request.
- Line 24 specifies the type name of the feature to be queried. In this case, it requests features of the “topp:states”.
- Lines 25 to 30 define the filter criteria for the query. On these lines, we use the PropertyIsLike filter, to retrieve all states that start with the word
North.
-
Press the Submit button to see the implemented changes.
- Note. For GeoServer 2.25.2 the Demo Request page has been improved to show response Headers, and provide the option to pretty print XML output.
Now, we are looking for the States with four-letter names, where the letter o appears at both the beginning and the end. This requires using a singleChar as a different mode of the “LIKE” operator that you see on the screen:
<ogc:Filter>
<PropertyIsLike wildCard="*" singleChar="_" escapeChar="\">
<PropertyName>STATE_NAME</PropertyName>
<Literal>O__o</Literal>
</PropertyIsLike>
</ogc:Filter>
Press the Submit button to see the implemented changes. As you can see, a state called Ohio was found that meets the conditions in this example.
To show the escapeChar mode, modify the names ‘Montana’ and ‘Minnesota’ to Monta*na and Minnesota* in QGIS. This will allow you to filter out special characters, such as asterisks or underscores, that you have used. Now, use the codes displayed on the screen:
<ogc:Filter>
<PropertyIsLike wildCard="*" singleChar="_" escapeChar="\">
<PropertyName>STATE_NAME</PropertyName>
<Literal>*ta\**</Literal>
</PropertyIsLike>
</ogc:Filter>
Press the Submit button to see the implemented changes. Note that, If the escapeChar is not used, the correct result may not be visible in the output; because the underscore is a special character.
You have the flexibility to modify the wildCard, singleChar, and escapeChar attributes based on your requirements. This allows for a more proper filtering experience. So, feel free to customize them and make the most of your filtering capabilities!
PropertyIsNull
This operator, allows you to query for features where a specific property or attribute, has a null value. In other words, it is used to filter the features based on the absence of a value in a particular property.
In this example, the query is looking for features in the topp:states layer, where the STATE_NAME attribute is null.
As an example of using this filter in a WFS getFeature request, use the following block codes to replace lines 26 to 29:
<PropertyIsNull>
<PropertyName>STATE_NAME</PropertyName>
</PropertyIsNull>
Press the Submit button. As you can see, there is no value returned in the output as a null value.
PropertyIsBetween
The PropertyIsBetween operator is a helpful tool that allows you to determine whether a particular property of a feature, is within a defined range of values. As an example of using this operator, select the WFS_getFeatureBetween1.1.xml request from the Request section.
Now the filters block code is as follows:
<ogc:Filter>
<ogc:PropertyIsBetween>
<ogc:PropertyName>topp:LAND_KM</ogc:PropertyName>
<ogc:LowerBoundary><ogc:Literal>100000</ogc:Literal></ogc:LowerBoundary>
<ogc:UpperBoundary><ogc:Literal>150000</ogc:Literal></ogc:UpperBoundary>
</ogc:PropertyIsBetween>
</ogc:Filter>
Press the Submit button.
Remember that PropertyIsBetween like other operators, is case-sensitive and the property name is specified as the first parameter to the operator. The minimum and maximum values of the range are specified as the second and third parameters, respectively.
In this session, we took a brief journey through the various types of filters, with a particular focus on “Value comparison operators in GeoServer”. If you want to access the complete tutorial, click on the link.
GeoServer 2.24.5 Release
GeoServer 2.24.5 release is now available with downloads (bin, war, windows), along with docs and extensions.
This is a maintenance release of GeoServer providing existing installations with minor updates and bug fixes. GeoServer 2.24.5 is made in conjunction with GeoTools 30.5, and GeoWebCache 1.24.5.
Thanks to Andrea Aime for making this release.
Release notes
Improvement:
- GEOS-11336 security-keycloak: upgrade keycloak version
- GEOS-11443 REST API does not take effect immediately due to 10 minute authentication cache
- GEOS-11463 WMS vector dimension validation should query only one feature and only for dimension attribute
- GEOS-11502 Permit resize on user/group/role palette textbox to allow for extra long role names
Bug:
- GEOS-11446 [INSPIRE] Incorrect behavior for unsupported languages
- GEOS-11453 Failure to look-up default value of custom dimensions on vector layers
- GEOS-11462 500 error thrown when double adding a user to a group via REST with JDBC user/group services
- GEOS-11484 DirectRasterRenderer is not respecting advancedProjectionHandling and continuosMapWrapping format_options
- GEOS-11493 Azure blob store may not get environment parameters from property file
Task:
- GEOS-11464 Update Jackson 2 libs from 2.17.1 to 2.17.2
For the complete list see 2.24.5 release notes.
Community Updates
Community module development:
- GEOS-11111 Open search for EO community module: STAC search page has wrong self link
Community modules are shared as source code to encourage collaboration. If a topic being explored is of interest to you, please contact the module developer to offer assistance.
About GeoServer 2.24 Series
Additional information on GeoServer 2.24 series:
- GeoServer 2.24 User Manual
- Control remote HTTP requests sent by GeoTools/GeoServer
- State of GeoServer 2.24.1 (foss4g-asia presentation)
- Multiple CRS authority support, planetary CRS
- Extensive GeoServer Printing improvements
- Upgraded security policy
Release notes: ( 2.24.5 | 2.24.4 | 2.24.3 | 2.24.2 | 2.24.1 | 2.24.0 | 2.24-RC )
