GeoServer Blog
GeoServer 2.27.0 Release
GeoServer 2.27.0 release is now available with downloads (bin, war, windows), along with docs and extensions.
This is a stable release of GeoServer recommended for production use. GeoServer 2.27.0 is made in conjunction with GeoTools 33.0, GeoWebCache 1.27.0, and ImageIO-EXT 1.4.15.
This release graduates the OGC API Features module to extension status, ensures all OGC services pass CITE compliance tests, and adds performance improvements to the catalog loader that significantly reduces startup times for large deployments. The release also includes Smart Data Loader override rules. This release addresses several security vulnerabilities, and enforces browser Content Security Policy for increased security.
Thanks to extensive community testing through our user forum, we’re confident in recommending this release for production use. Check update notes for specific instructions.
Thanks to Gabriel Roldan (Camptocamp) and Jody Garnett (GeoCat) for making this release and to all contributors who helped with this release cycle.
Community Testing
This release cycle featured an extensive community testing effort, with our new discourse communication channels playing a central role in pre-release validation.
Testers helped identify and resolve several important issues:
- Performance Improvements: Daniel Calliess verified faster startup times and validated the GeoFence plugin functionality.
- Security Enhancements: Georg and Roar Brænden provided detailed feedback on the new Content Security Policy (CSP) implementation, helping refine the upgrade instructions.
- Catalog Robustness: Andrea tested the new parallel catalog loader across various data directory configurations, identifying and helping resolve concurrency edge cases.
- Documentation: Emanuele Tajariol collaborated with Daniel to update GeoFence plugin documentation.
- Standards Implementation: Landry Breuil validated the OGC API Features extension on behalf of the geOrchestra community.
The GeoServer team is grateful to all community members who participated in this testing effort. Their feedback was instrumental in addressing issues before release and ensuring a smooth upgrade experience for users.
Special thanks to Andrea, Jody, Peter, and Gabriel for their diligent work reviewing feedback and addressing issues throughout the preflight testing period.
Security Considerations
This release addresses several security vulnerabilities, and is a recommended upgrade for production systems.
- CVE-2025-30145 Denial-of-service (DoS) Vulnerability in Jiffle process (High)
- CVE-2025-27505 Missing Authorization on REST API Index (Moderate)
- CVE-2024-29198 Unauthenticated SSRF via TestWfsPost (Moderate)
- CVE-2024-40625 Coverage REST API Server Side Request Forgery (Moderate)
- CVE-2025-21621 Reflected Cross-Site Scripting (XSS) vulnerability in WMS GetFeatureInfo HTML format (Moderate)
- CVE-2025-58360 Unauthenticated XML External Entities (XXE) via WMS GetMap operation (High)
The use of the CVE system allows the GeoServer team to reach a wider audience than blog posts. See project security policy for more information on how security vulnerabilities are managed.
OGC API FeaturesService Extension
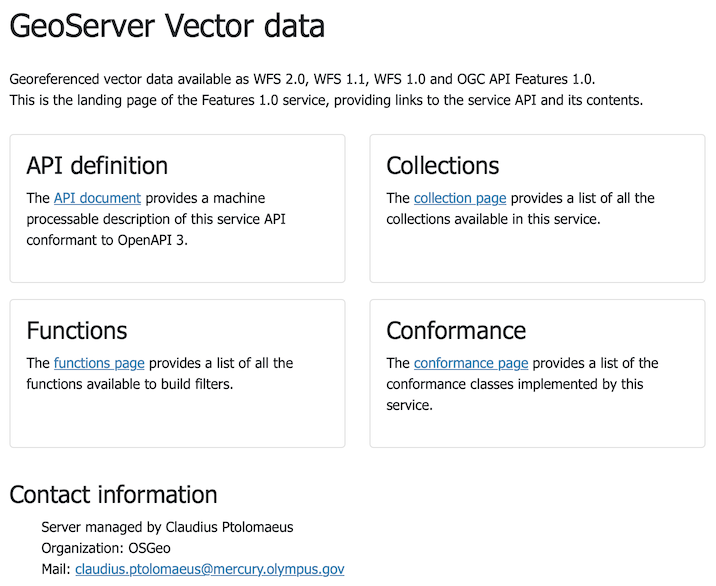
The OGC API Features module has officially graduated from community status to become a supported GeoServer extension. This implementation of the modern, web-friendly OGC API - Features standard provides a RESTful API alternative to traditional WFS services.
Key capabilities include:
- Feature collection discovery and access
- Spatial and attribute filtering using CQL2
- Multiple output formats (GeoJSON, HTML, etc.)
- Service-level operations across multiple collections
This service operates alongside the existing WFS services:
-
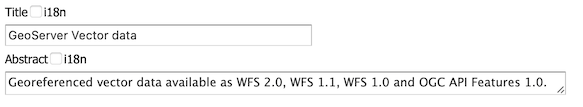
Update the WFS Settings title and description appropriately.
-
This information is used for the service landing page:
-
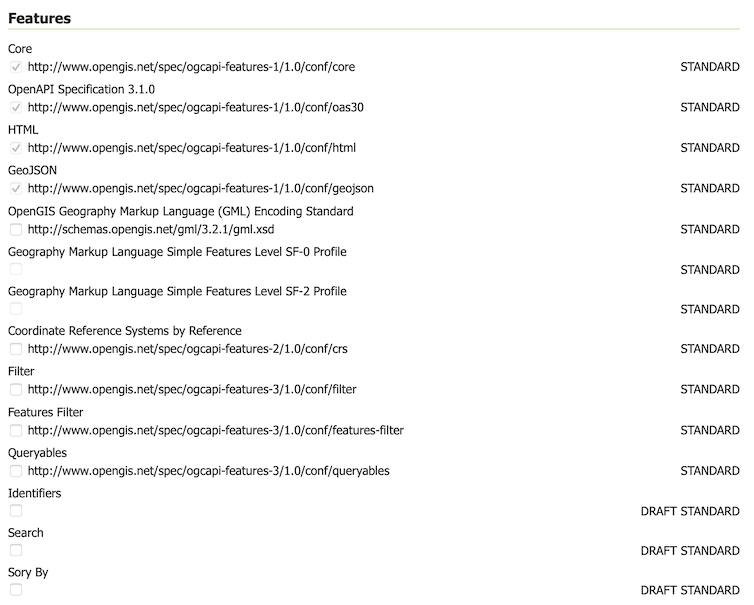
GeoServer has not previously included draft or work-in-progress development - preferring to make such functionality available as community modules for developers to collaborate. However OGC API - Features specification is defined in a modular fashion, and accommodates the idea of both draft and community standards.
To configure enable/disable “conformances” for Features, CQL2, and ECQL.
-
For more information on OGC API support in GeoServer:
- OGC API Service Configuration (User Manual)
- Configuration of OGC API - Features module (User Manual)
This graduation is the result of a collaborative code sprint with developers from Camptocamp, GeoSolutions, and GeoCat joining forces. As part of this effort, the module now passes OGC CITE compliance tests, ensuring proper interoperability with other OGC-compliant systems.
Special thanks to the French “Commissariat général au développement durable du Ministère chargé de l’Ecologie” for sponsoring this work as part of the Collectif Interopérabilité et mise en Commun de Composants Logiciels pour les plateformes de données (CICCLO) project.
For more information, and the extension user docs.
- GSIP-230 OGC API Features Extension
- GEOS-11627 OGCAPI FeatureService Extension
OGC CITE Compliance
A significant effort has been made to ensure GeoServer passes the OGC Conformance and Interoperability Test and Evaluation (CITE) compliance tests across all supported services. This work improves the quality and interoperability of GeoServer with other OGC-compliant systems.
Restoring CITE Compliance has been a project goal for a number of years, and an ongoing sponsorship goal for the GeoServer project. Many thanks to prior sponsors of this activity including Gaia3D, and OSGeo:UK.
We are pleased to share that GeoServer now passes all the OGC CITE compliance tests available for the services it supports. Passing OGC CITE tests involved fixing numerous issues related to exception handling, version negotiation, and service behavior.
Special thanks to Andrea Aime for leveraging, extending, and improving the OGC CITE conformance testing infrastructure that was developed during the OGC API Features work, and methodically applying it to ensure all GeoServer services now pass their respective compliance tests.
While official certification from the OGC is still pending at the time of writing, the process is underway and we anticipate formal recognition of GeoServer in the coming days.
Thanks to Peter Smythe (AfriGIS) and Angelos Tzotsos for working with Open Source Geospatial Foundation to provide access to the CITE Certification process. Once certification is granted, we will update this post and home page with a “live logo” to reflect our official status.
- GEOS-11729 Pass WCS 1.0 certification OGC CITE tests
- GEOS-11730 Pass WCS 1.1 certification OGC CITE tests
- GEOS-11780 Pass WCS 2.0 certification OGC CITE tests
- GEOS-11731 Pass WFS 1.0 certification OGC CITE tests
- GEOS-11732 Pass WFS 1.1 certification OGC CITE tests
- GEOS-11733 Pass WFS 2.0 certification OGC CITE tests
- GEOS-11734 Pass WMS 1.1 certification OGC CITE tests
- GEOS-11735 Pass WMS 1.3 certification OGC CITE tests
- GEOS-11779 Pass WMTS 1.0 certification OGC CITE tests
- GEOS-11736 Pass OGC API Features 1.0 certification OGC CITE tests
- GEOS-11752 Pass GeoTIFF 1.1 certification OGC CITE tests
- GEOS-11753 Pass GPKG 1.2 certification OGC CITE tests
Content Security Policy Enforced
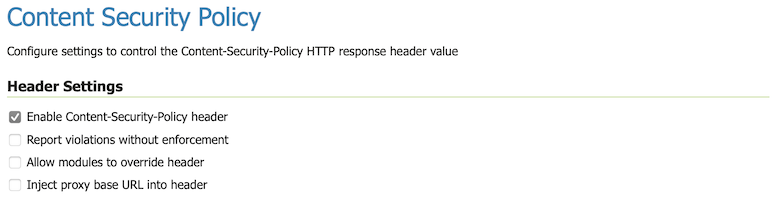
The use of Content Security Policy (CSP) headers is an additional safety precaution introduced by your browser to mitigate cross-site scripting and clickjacking attacks.
GeoServer 2.27.0 pages now include a Content Security Policy, limiting expected browser interactions to increase security.
-
Before updating double check your
PROXY_BASE_URLsetting is correct.This is a common mistake blocked by the new CSP policy.
-
It is expected that the web administration console functions correctly, along with extensions and community modules.
With these improved CSP safety measures GeoServer may now detect vulnerabilities in your environment that were previously undetected.
If you run into any problems, troubleshooting instructions are available in the user manual.
-
Additional tools are available for administrators seeking greater control.
Thanks to Steve Ikeoka for his dedication to this activity.
- GSIP 227 Content-Security-Policy Headers
- GEOS-11346 Add a configurable Content-Security-Policy header
- GEOS-11698 Update GeoServer User Interface Troubleshooting Guidance
- GEOS-11585 Patch Spectrum to work with Wicket’s CSP
- GEOS-11586 Patch CodeMirror to work with Wicket’s CSP
- GEOS-11669 Patch jscolor to work with Wicket’s CSP
Faster Catalog Loading
GeoServer 2.27.0 includes significant performance improvements for server startup with the promotion of the “datadir catalog loader” from a community module to the GeoServer core. This enhanced loader dramatically improves startup times for deployments with large data directories through parallel processing.
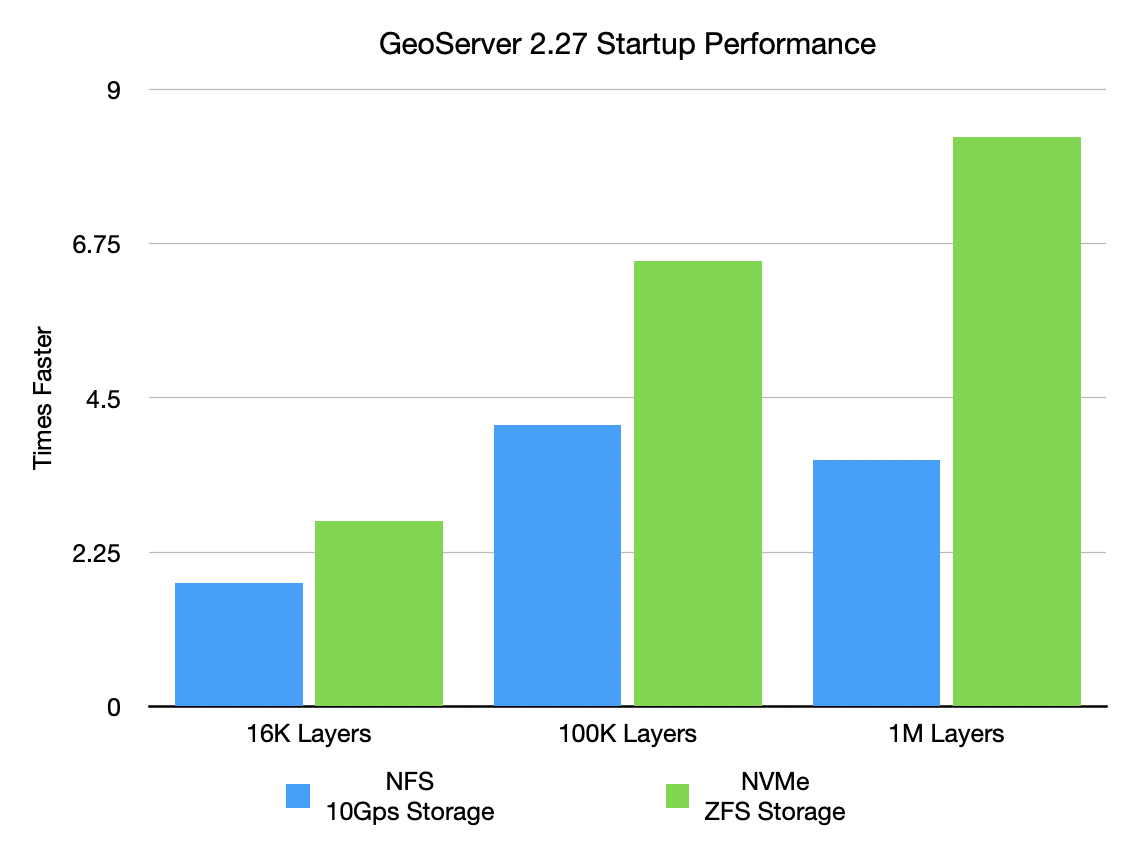
The performance gains are substantial, as shown by these benchmark results:
NFS/10Gbps Storage:
- 16K layers: reduced from 5.8s to 3.3s (1.8× faster)
- 100K layers: reduced from 1.9min to 28.3s (4.1× faster)
- 1M layers: reduced from 21.3min to 5.9min (3.6× faster)
NVMe Gen5/ZFS Storage:
- 16K layers: reduced from 3.5s to 1.3s (2.7× faster)
- 100K layers: reduced from 21.2s to 3.2s (6.5× faster)
- 1M layers: reduced from 3.4min to 24.6s (8.3× faster)
The new loader uses work-stealing thread pools for catalog processing while ensuring thread safety. This enhancement is particularly valuable for large enterprise deployments where startup time has been a bottleneck.
The loader is enabled by default but can be disabled or tuned if needed as explained in the data directory documentation.
- GSIP-231 Promote data_dir catalog loader to core
- GEOS-11284 Promote community module “datadir catalog loader” to core
File System Sandbox Isolation
A file system sandbox is used to limit access for GeoServer Administrators and Workspace Administrators to specified file folders.
-
A system sandbox is established using
GEOSERVER_FILESYSTEM_SANDBOXapplication property, and applies to the entire application, limiting GeoServer administrators to the<sandbox>folder, and individual workspace administrators into isolated<sandbox>/<workspace>folders. -
A regular sandbox can be configured from the Security > Data screen, and is used to limit individual workspace administrators into
<sandbox>/<workspace>folders to avoid accessing each other’s files.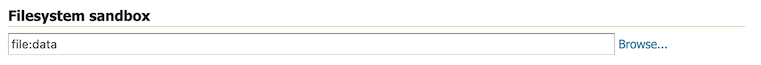
Thanks to Andrea (GeoSolutions) for this important improvement at the bequest of Munich RE.
MapML Enhancement
The MapML extension continues to receive significant updates.
Tiled Coordinate Reference Systems can now be managed with a new MapML TCRS Settings page, available in the Admin Console Settings section:
The MapML TCRS Settings page provides a selector containing available GridSets. The administrator can select GridSets from the left list that will be converted to TiledCRSs.
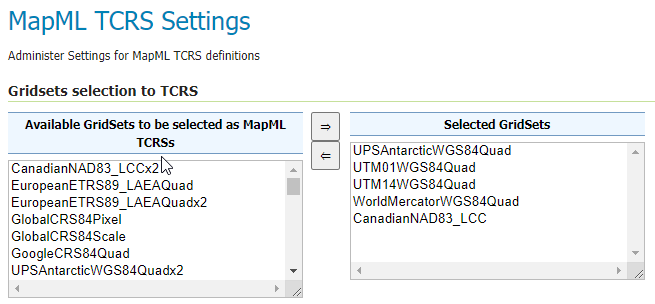
Check out the documentation for more insights.
These changes provide better integration and more powerful capabilities for creating web maps with MapML.
- GEOS-11561 Client-Delegating MapML Proxy
- GEOS-11577 Rename MapML <layer-> to <map-layer>, rename viewer bundle to mapml.js
- GEOS-11605 MapML Support custom TCRS projections from existing GridSets
- GEOS-11666 Update MapML viewer to latest release 0.16.0
Smart Data Loader Enhancements
The Smart Data Loader has been improved with override rules, making it more flexible for data management scenarios:
The Smart Data Loader plugin automates the creation of XSD schemas and App-Schema mapping files, significantly simplifying the configuration of complex feature data in GeoServer.
With the new override rules capability, you can now customize how database tables are mapped to feature types without modifying the database schema, providing greater control and flexibility when working with complex or legacy data structures.
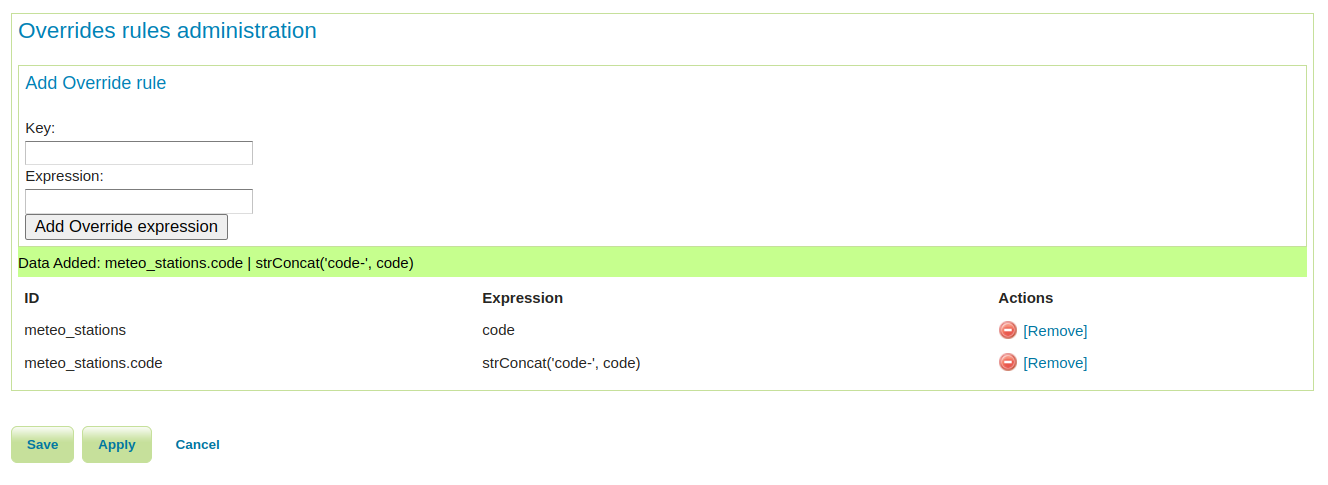
For more details on using Smart Override Rules, see the official documentation.
- GEOS-11741 Enhancing Smart Data Loader with Override Rules
- GEOS-11691 Smart data loader accepts bigint and bigserial but not int8 postgresql type alias
GeoFence Improvements
The GeoFence extension has received several significant improvements:
These improvements make GeoFence more flexible and powerful for implementing fine-grained security policies.
- GEOS-11702 GeoFence: major libs update
- GEOS-11704 GeoFence: filter rule list by IP address
- GEOS-11705 GeoFence: make rules valid within a date range
- GEOS-11526 GeoFence: slow GeoServer response when there are many roles and layergroups
Performance Improvements
Several performance improvements have been implemented in this release:
- GEOS-11580 Improve embedded GWC meta-tiling performance
- GEOS-11766 Speed up CRS and store factory lookups during catalog loading
- GEOS-11722 Coverage view reader partially ignores multithreaded loading
- GEOS-11739 Excessive memory usage for WMS KML output format
- GEOS-11760 Fix a potential OOM in the KML transformation
WPS Improvements
Several improvements have been made to the Web Processing Service implementations:
- GEOS-11564 WPS calls to internal WFS will handle requests with version=2.0.0
- GEOS-11783 Longitudinal profile process now allows for input chaining
- GEOS-11784 The longitudinal profile process limits the number of points it can extract
- GEOS-11785 The longitudinal profile process now respects cancellation
- GEOS-11786 General performance improvements for the longitudinal profile process
Other Improvements
- GEOS-11468 Coverage REST API URL Checks
- GEOS-11562 Default Gzip filter setting in web.xml does not compress application/javascript
- GEOS-11578 WMTS Multidim extension, allow usage of a sidecar in a separate store
- GEOS-11603 KML download mode now shows layer titles
- GEOS-11612 Add system property support for Proxy base URL -> use headers activation
- GEOS-11613 Increase control-flow logging admin visibility in logs
- GEOS-11624 Split Geopackage extension into separate modules to reduce dependencies
- GEOS-11625 Add “Challenge Anonymous Sessions” Option to AuthKey Filter
- GEOS-11645 Control FreeMarker template access
- GEOS-11654 Fix multiline strings that are missing a space between the lines
- GEOS-11677 Hide version info on GWC home page
Library Updates
GeoServer 2.27.0 includes updates to many core libraries:
- GEOS-11770 Update to jai-ext 1.1.31
- GEOS-11771 Update to Imageio-EXT 1.4.15
- GEOS-11590 Upgrade log4j to 2.24.1 and slf4j to 2.0.16
- GEOS-11608 Update Bouncy Castle Crypto package from bcprov-jdk15on:1.69 to bcprov-jdk18on:1.79
- GEOS-11609 Bump XStream from 1.4.20 to 1.4.21
- GEOS-11685 Bump jetty.version from 9.4.56.v20240826 to 9.4.57.v20241219
- GEOS-11631 Update MySQL driver to 9.1.0
- GEOS-11743 Upgrade Oracle JDBC driver (ojdbc) from 8 to 11
- GEOS-11754 Update to mapfish-print-v2 2.3.3
- GEOS-11763 Update jai-ext to latest version (1.1.30)
Bug Fixes
Many bugs have been fixed in this release, including:
- GEOS-4533, GEOS-7967 Fixed WPS demo builder chaining issues
- GEOS-11494 WFS GetFeature request with a propertyname parameter fails when layer attributes are customized
- GEOS-11524 CSW: default queryables mapping not generated
- GEOS-11540 OGC API queryables features call not working in JSON
- GEOS-11607 KML WMS GetMap is performing a heavy database load query
- GEOS-11620 Smart Data Loader plugin produces a Mapping file data source definition and tries to establish a connection pool, but fails
- GEOS-11636 Store panels won’t always show feedback in target panels
- GEOS-11649 Welcome page per-layer is not respecting global service enablement
- GEOS-11658 Time editor dumps stack trace in UI if the start or end time values are intervals
- GEOS-11664 Update REST security paths
- GEOS-11667 Make WMTS work in strict cite compliance mode
- GEOS-11668 WMTS home page capabilities link uses 1.1.1 as the version, and the wrong version negotiation approach
- GEOS-11684 GDAL no longer included in Docker image
- GEOS-11762 Feature Templates by feature type can not be listed via GeoServer Rest API
- GEOS-11792 Default Service Capabilities shown on initial start with no workspaces
- GEOS-11796 Deadlocks During GeoServer Startup When Loading Style Group Layer Groups
Community Module Updates
Community modules are shared as source code to encourage collaboration. If a topic being explored is of interest to you, please contact the module developer to offer assistance.
Community module development:
- GEOS-11651 Support env parametrization on OIDC filter
- GEOS-11781 Community cleanup fall 2024
- Removed abandoned community modules:
- GEOS-11641 Remove the abandoned community module webservice-test
- GEOS-11642 Remove the gwc-distributed community module
Full Release Notes
For the complete list of changes, see 2.27.0 release notes.
About GeoServer 2.27 Series
Additional information on GeoServer 2.27 series:
- GeoServer 2.27 User Manual
- GeoServer 2025 Roadmap
- Content-Security-Policy Headers
- OGCAPI Features Extension
- File system access isolation
- Promote data dir catalog loader to core
Release notes: (2.27.0)
GeoServer 2.22.6 Release
GeoServer 2.22.6 release is now available with downloads (bin, war, windows), along with docs and extensions.
This series has previously reached end-of-life, with this release issued to address a security vulnerability. Please apply this update as a mitigation measure only, and plan to upgrade to a stable or maintenance release of GeoServer. GeoServer 2.22.6 is made in conjunction with GeoTools 28.6.
Thanks to Jody Garnett (GeoCat) and Andrea Aime (GeoSolutions) for making this release.
Security Considerations
This release addresses security vulnerabilities for those operating in a Java 8 environment:
-
CVE-2024-36401 Remote Code Execution (RCE) vulnerability in evaluating property name expressions (Critical)
For more information see the following statement.
See project security policy for more information on how security vulnerabilities are managed.
Java 8 End-of-life
This GeoServer 2.22.6 is archived and has reached end-of-life. This release uses recent GeoTools 28.6 Java 8 artifacts addressing CVE-2024-36404.
All future releases will require a minimum of Java 11.
Release notes
Improvement:
- GEOS-11102 Allow configuration of the CSV date format
- GEOS-11116 GetMap/GetFeatureInfo with groups and view params can with mismatched layers/params
- GEOS-11155 Add the X-Content-Type-Options header
- GEOS-11246 Schemaless plugin performance for WFS
Bug:
- GEOS-11138 Jetty unable to start cvc-elt.1.a / org.xml.sax.SAXParseException
Task:
- GEOS-11318 Upgrade postgresql from 42.6.0 to 42.7.2
For the complete list see 2.22.6 release notes.
Community Updates
Community module development:
- GEOS-11412 Remove reference to JDOM from JMS Cluster (as JDOM is no longer in use)
Community modules are shared as source code to encourage collaboration. If a topic being explored is of interest to you, please contact the module developer to offer assistance.
About GeoServer 2.22 Series
Additional information on GeoServer 2.22 series:
- GeoServer 2.22 User Manual
- Update Instructions
- Metadata extension
- CSW ISO Metadata extension
- State of GeoServer (FOSS4G Presentation)
- GeoServer Beginner Workshop (FOSS4G Workshop)
- Welcome page (User Guide)
Release notes: ( 2.22.6 | 2.22.5 | 2.22.4 | 2.22.3 | 2.22.2 | 2.22.1 | 2.22.0 | 2.22-RC | 2.22-M0 )
GeoServer 2.25.6 Release
GeoServer 2.25.6 release is now available with downloads (bin, war, windows), along with docs and extensions.
This series has now reached end-of-life, and it is recommended to plan an upgrade to 2.26.x or the upcoming 2.27.0 soon.
GeoServer 2.25.6 is made in conjunction with GeoTools 31.6, and GeoWebCache 1.25.4.
Thanks to Jody Garnett (GeoCat) and Andrea Aime (GeoSolutions) for making this release.
Security Considerations
This release addresses several security vulnerabilities, and is a recommended upgrade for production systems.
-
CVE-2025-27505 Missing Authorization on REST API Index (Moderate)
-
CVE-2024-38524 GWC Home Page exposes sensitive server information (Moderate)
-
Unauthenticated XML External Entities (XXE) via WMS GetMap operation (High)
See project security policy for more information on how security vulnerabilities are managed.
Release notes
Improvement:
- GEOS-11651 Support env parametrization on OIDC filter
- GEOS-11652 Externalize printing configuration folder
- GEOS-11677 Hide version info on GWC home page
Bug:
- GEOS-10844 Exclude xml-apis from build
- GEOS-11649 welcome page per-layer is not respecting global service enablement
- GEOS-11664 Update REST security paths
- GEOS-11672 GWC virtual services available with empty contents
- GEOS-11690 Bug in Externalize printing configuration folder
- GEOS-11694 OpenID connect: allow caching authentication when an expiration is declared in the access token
- GEOS-11696 AdminRequestCallback not loaded due to spring bean name conflict
- GEOS-11700 GeoFence fails in recognizing some caller IP address
- GEOS-11707 Ogr2OgrWfsTest test failures with GDAL 3.10.1
- GEOS-11711 Clickhouse DGGS stores fails to aggregate on dates
- GEOS-11713 Concurrent LDAP builds fail on Jenkins
- GEOS-11715 STAC sortby won’t work with “properties.” prefixed names
- GEOS-11716 WFS POST requests fail if a layer is misconfigured
Task:
- GEOS-11650 Update dependencies for monitoring-kafka module
- GEOS-11659 Apply Palantir Java format on GeoServer
- GEOS-11671 Upgrade H3 dependency to 3.7.3
- GEOS-11682 Add tests for WMS SLD XML request reader
- GEOS-11685 Bump jetty.version from 9.4.56.v20240826 to 9.4.57.v20241219
- GEOS-11701 Update JAI-Ext to 1.1.28
For the complete list see 2.25.6 release notes.
Community Updates
Community module development:
- GEOS-11686 Clickhouse DGGS stores cannot properly read dates
- GEOS-11687 OGC API packages contain gs-web-core
Community modules are shared as source code to encourage collaboration. If a topic being explored is of interest to you, please contact the module developer to offer assistance.
About GeoServer 2.25 Series
Additional information on GeoServer 2.25 series:
- GeoServer 2.25 User Manual
- GeoServer 2024 Roadmap Plannings
- Raster Attribute Table extension
- Individual contributor clarification
Release notes: ( 2.25.6 | 2.25.5 | 2.25.4 | 2.25.3 | 2.25.2 | 2.25.1 | 2.25.0 | 2.25-RC )
Powerful SLD Styles & Filters in GeoServer
GeoSpatial Techno is a startup focused on geospatial information that is providing e-learning courses to enhance the knowledge of geospatial information users, students, and other startups. The main approach of this startup is providing quality, valid specialized training in the field of geospatial information.
( YouTube | LinkedIn | Facebook | X )
Powerful SLD Styles and Filters in GeoServer
In this session, we’ll explore GeoServer SLD styles and filters and highlight their practical and versatile uses. If you want to access the complete tutorial, click on the link.
Introduction
Filters in GeoServer are essential for controlling map data display, allowing users to set conditions for data inclusion. By integrating these filters into a Styled Layer Descriptor (SLD), users can customize maps based on specific attribute values or spatial areas. This customization enables the creation of visually informative and meaningful maps that effectively showcase data.
Several types of filters can be used in GeoServer styling, such as Comparison operators , Spatial operators , Logical operators and Arithmetic operators.
Note. This video was recorded on GeoServer 2.22.4, which is not the most up-to-date version. We encourage all users to use the stable series, currently 2.28.x. To ensure you have the latest release, please visit this link and avoid using older versions of GeoServer.
Note. In all examples in this blog post, we utilize the topp:states layer.
Comparison Operators
These operators allow users to filter data by focusing on non-spatial attributes of a feature, selecting specific values within a field, or defining a range of values. This functionality helps refine search results within a dataset for more precise data analysis.
The Comparison operators include: Binary comparison operators and Value comparison operators.
The binary comparison operators are: PropertyIsEqualTo , PropertyIsNotEqualTo , PropertyIsLessThan , PropertyIsLessThanOrEqualTo , PropertyIsGreaterThan and PropertyIsGreaterThanOrEqualTo.
To learn how to use various filters for creating a custom SLD style in GeoServer, follow these steps:
- Navigate to the Styles page from the Data section, then click on Add a new style link.
- In the Name field, type your desired name, such as
Comparison_lessThan. - Select Polygon from the list of default styles, then click the Generate link.
-
Type the new title on line 13, and press the ‘Enter’ key at the end of the line. Then, add the following block codes to the new line:
<ogc:Filter> <ogc:PropertyIsLessThan> <ogc:PropertyName>PERSONS</ogc:PropertyName> <ogc:Literal>1000000</ogc:Literal> </ogc:PropertyIsLessThan> </ogc:Filter> - Press the Validate button to check if you have misspelled anything. If there are no errors, press the Apply button.
- Switch to the Layer Preview tab and click the layer name above the preview box and select
topp:stateslayer.
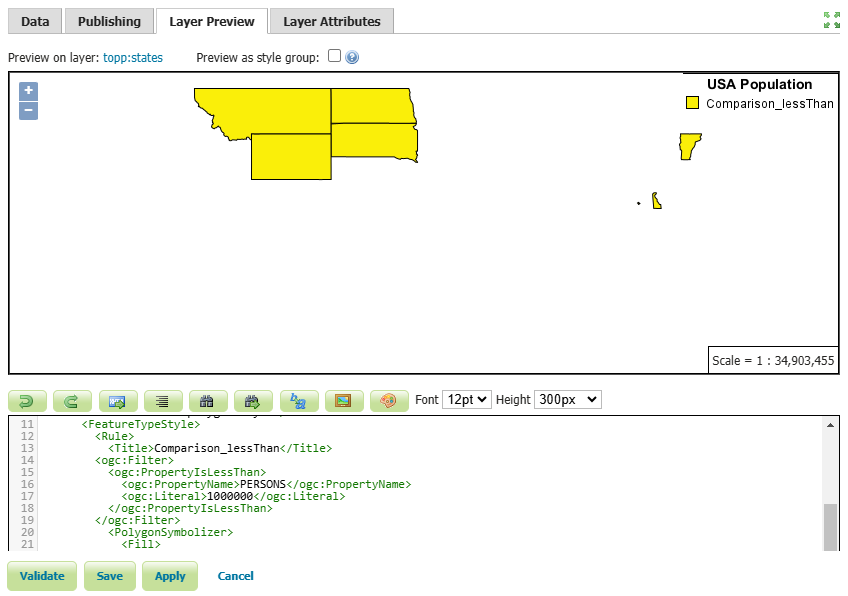 In this example, we have created a style for states with a population of less than one million.
In this example, we have created a style for states with a population of less than one million.
- Press the Save button.
Other available comparison operators, known as the value comparison operators include: PropertyIsLike , PropertyIsNull, and PropertyIsBetween.
To use the PropertyIsLike operator in a new style, follow these steps:
-
Click on Add a new style link, then enter
Comparison_likein the Name field. -
Select Comparison_lessThan from the existing styles, then click the Copy link.
-
To filter the states that include
newin their name, modify the existing codes using the following codes:<ogc:Filter> <ogc:PropertyIsLike wildCard="%" singleChar="_" escape="!"> <ogc:PropertyName>STATE_NAME</ogc:PropertyName> <ogc:Literal>%new%</ogc:Literal> </ogc:PropertyIsLike> </ogc:Filter> -
Additionally, insert the following block of code on line 30 to display the names of the states as well.
<TextSymbolizer> <Label> <ogc:PropertyName>STATE_NAME</ogc:PropertyName> </Label> <VendorOption name="maxDisplacement">50</VendorOption> </TextSymbolizer> -
Press the Validate button to check if you have misspelled anything. If there are no errors, press the Apply button.
-
Switch to the Layer Preview tab and click the layer name above the preview box and select
topp:stateslayer.
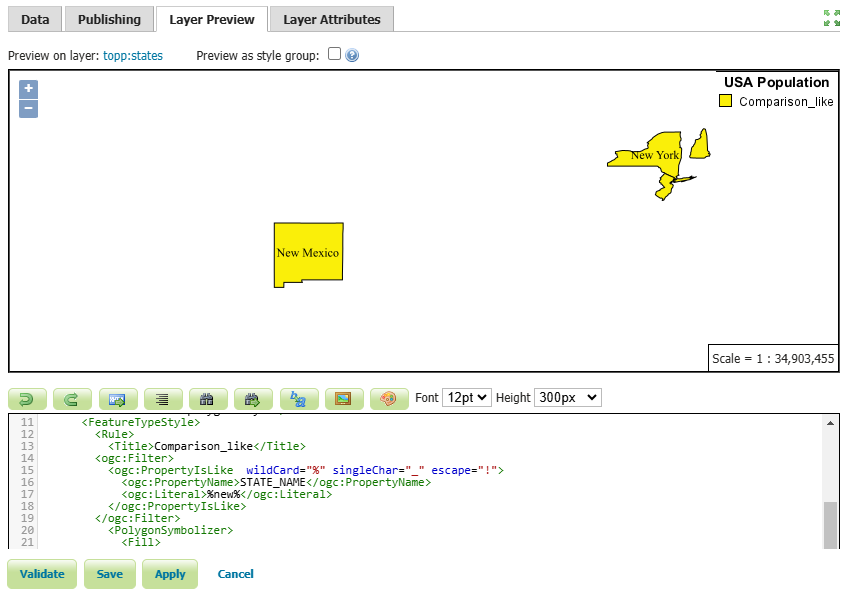
In this example, we filtered the states that have the word new in their name, such as: New York , New Jersey , New Hampshire and New Mexico.
- Press the Save button.
Spatial Operators
These operators allow users to filter data based on its spatial location. This can include filtering data based on its proximity to a specific point, within a specific area or boundary, or in relation to other spatial features.
Some common spatial operators include: Within , Contains , Intersects , BBOX , etc. For a comprehensive list of all the spatial operators, please visit this link
Follow these steps to use the Intersects filter in a new style:
- Click on Add a new style link, then enter
spatial_intersectsin the Name field. - Select
comparison_likefrom the existing styles, then click the Copy link. -
Edit the codes using the following codes:
<ogc:Filter xmlns:gml="http://www.opengis.net/gml"> <ogc:Intersects> <ogc:PropertyName>the_geom</ogc:PropertyName> <gml:LineString> <gml:coordinates>-112.5,34.7 -106.8,36.7 -100.5,36.8 -97.4,42.4</gml:coordinates> </gml:LineString> </ogc:Intersects> </ogc:Filter> - Press the Validate button to check if you have misspelled anything. If there are no errors, press the Apply button.
- Switch to the Layer Preview tab and select
topp:stateslayer.
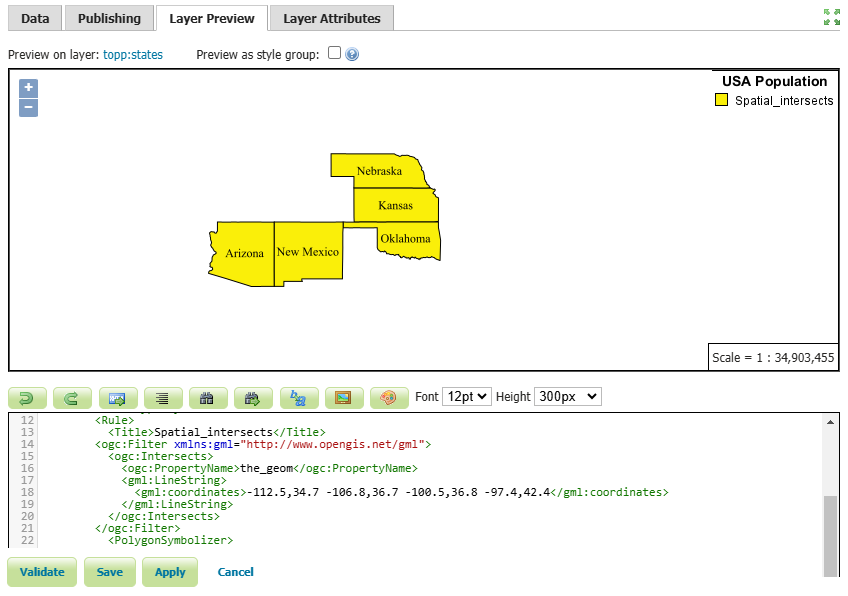
The states that intersect with a LineString, determined by the specified coordinates, include Arizona, New Mexico, Oklahoma, Kansas and Nebraska.
- Press the Save button.
Logical Operators
Logical operators are used to set conditions for applying specific style rules to features. They allow users to create complex rules based on various attributes and conditions. In GeoServer, the key logical operators are AND, OR, and NOT.
- AND: Both specified conditions must be true for the style rule to be applied.
- OR: At least one of the specified conditions must be true for the style rule to be applied.
- NOT: The style rule will not apply to features that do not meet the specified condition.
Here’s an example of how to use the AND operator to filter a SLD based on two conditions.
-
Click on Add a new style link, then enter
logical_andin the Name field. -
Select
spatial_intersectsfrom the existing styles, then click the Copy link. -
Edit the codes using the block codes below:
<ogc:Filter xmlns:gml="http://www.opengis.net/gml"> <ogc:And> <ogc:BBOX> <ogc:PropertyName>the_geom</ogc:PropertyName> <gml:Box> <gml:coord> <gml:X>-105</gml:X> <gml:Y>35</gml:Y> </gml:coord> <gml:coord> <gml:X>-90</gml:X> <gml:Y>45</gml:Y> </gml:coord> </gml:Box> </ogc:BBOX> <ogc:PropertyIsBetween> <ogc:PropertyName>PERSONS</ogc:PropertyName> <ogc:LowerBoundary> <ogc:Literal>3000000</ogc:Literal> </ogc:LowerBoundary> <ogc:UpperBoundary> <ogc:Literal>5000000</ogc:Literal> </ogc:UpperBoundary> </ogc:PropertyIsBetween> </ogc:And> </ogc:Filter> - Press the Validate button to check if you have misspelled anything. If there are no errors, press the Apply button.
- Switch to the Layer Preview tab and select
topp:stateslayer.
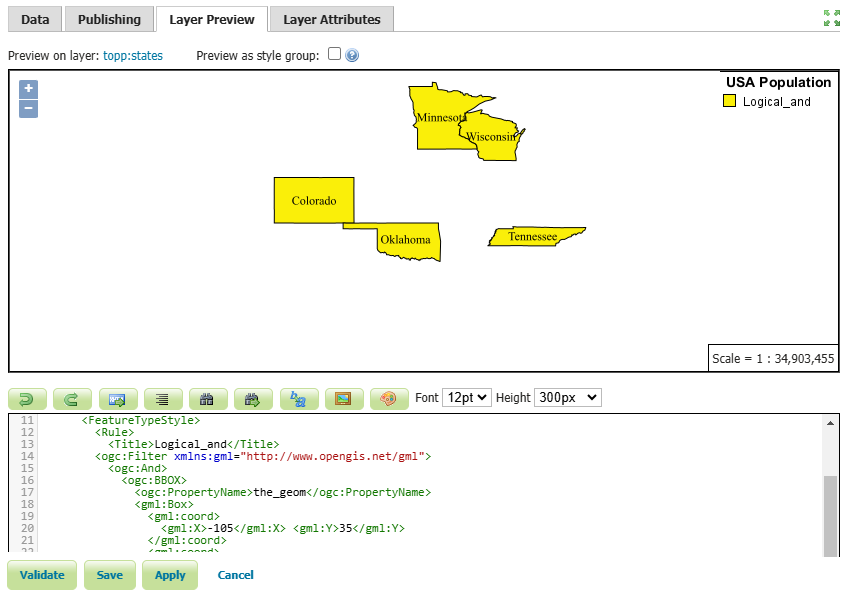
In this example, the states that intersect a certain bounding box and have a population between 3 million and 5 million have been filtered. The states that meet these criteria are Colorado, Oklahoma, Tennessee, Minnesota and Wisconsin.
- Press the Save button.
Arithmetic operators
Arithmetic operators enable users to create custom visualizations through mathematical equations and expressions, allowing them to effectively convey their data visually on maps.
The available arithmetic operators include: Add , Sub , Mul and Div.
For example, you can use arithmetic operators to create a proportional symbol map, where the size of point symbols is based on a numeric attribute value. By dividing the attribute value by a constant factor, you can control the size of the symbols accordingly.
Here’s an example of how to use this operator in GeoServer:
-
Click on Add a new style link, then enter
arithmetic_divin the Name field. -
Select Polygon from the list of default styles, then click the Generate link.
-
Enter the following code snippet on line 26:
<Rule> <Name/> <Title>PERSONS Symbol</Title> <PointSymbolizer> <Geometry> <ogc:Function name="centroid"> <ogc:PropertyName>the_geom</ogc:PropertyName> </ogc:Function> </Geometry> <Graphic> <Mark> <WellKnownName>circle</WellKnownName> <Fill> <CssParameter name="fill">#FF0000</CssParameter> </Fill> <Stroke> <CssParameter name="stroke">#000000</CssParameter> <CssParameter name="stroke-width">1</CssParameter> </Stroke> </Mark> <Size> <ogc:Div> <ogc:PropertyName>PERSONS</ogc:PropertyName> <ogc:Literal>1000000</ogc:Literal> </ogc:Div> </Size> </Graphic> </PointSymbolizer> </Rule>
In this example, we have defined two rules. The first rule is to display the simple polygons representing the states, while the second rule is to create circular symbols based on the population of each state.
We used the Centroid function to assign a symbol to each state, and place it exactly in the center of each polygon. In addition, we divided the Persons attribute by one million to ensure a proportional representation of the symbol size to the polygons.
-
Press the Validate button to check if you have misspelled anything. If there are no errors, press the Apply button.
-
Switch to the Layer Preview tab and select
topp:stateslayer.
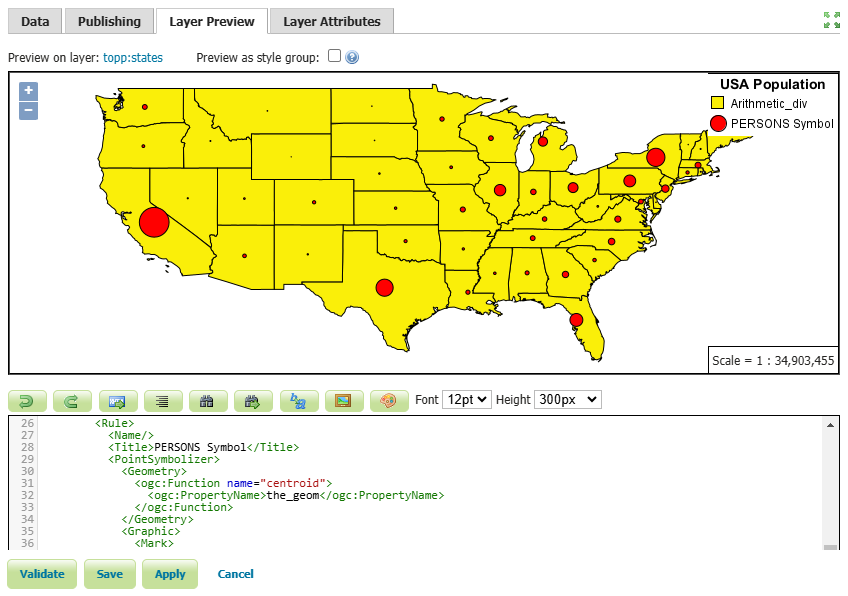
As you can see, we have scaled the point size based on the PERSONS attribute. This makes the symbol larger for larger population values like California, New York and Texas and the symbol smaller for smaller population values like Wyoming.
- Press the Save button.
In this session, we took a brief journey to explore SLD styles and various filters in GeoServer. If you want to access the complete tutorial, click on the link.
GeoServer 2.26.2 Release
GeoServer 2.26.2 release is now available with downloads (bin, war, windows), along with docs and extensions.
This is a stable release of GeoServer recommended for production use. GeoServer 2.26.2 is made in conjunction with GeoTools 32.2, GeoWebCache 1.26.2, and ImageIO-Ext 1.4.14.
Thanks to Jody Garnett for making this release.
Security Considerations
This release addresses security vulnerabilities and is recommended.
- CVE-2024-38524 GWC Home Page exposes sensitive server information (Moderate)
- CVE-2025-58360 Unauthenticated XML External Entities (XXE) via WMS GetMap operation (High)
See project security policy for more information on how security vulnerabilities are managed.
File System Sandbox Isolation
A file system sandbox is used to limit access for GeoServer Administrators and Workspace Administrators to specified file folders.
-
A system sandbox is established using
GEOSERVER_FILESYSTEM_SANDBOXapplication property, and applies to the entire application, limiting GeoServer administrators to the<sandbox>folder, and individual workspace administrators into isolated<sandbox>/<workspace>folders. -
A regular sandbox can be configured from the Security > Data screen, and is used to limit individual workspace administrators into
<sandbox>/<workspace>folders to avoid accessing each other’s files.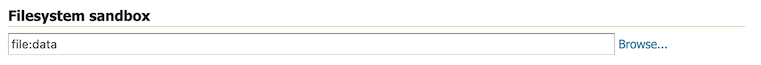
Thanks to Andrea (GeoSolutions) for this important improvement at the bequest of Munich RE.
Developer Updates
Palantir formatter
A nice update for GeoServer developers is an updated formatter that is both wider at 120 columns, and plays well with the use of lamda expressions.
List<TemplateBuilder> filtered = children.stream()
.filter(b -> b instanceof DynamicValueBuilder || b instanceof SourceBuilder)
.collect(Collectors.toList());
Thanks to Andrea for this improvement, and coordinating the change across all active branches.
Release notes
New Features:
- GEOS-11616 GSIP 229 - File system access isolation
- GEOS-11644 Introducing the rest/security/acl/catalog/reload rest endpoint
Improvement:
- GEOS-11612 Add system property support for Proxy base URL -> use headers activation
- GEOS-11615 Update to Imageio-EXT 1.4.14
- GEOS-11683 MapML WMS Features Coordinate Precision Should be adjusted based on scale
Bug:
- GEOS-11636 Store panels won’t always show feedback in target panels
- GEOS-11494 WFS GetFeature request with a propertyname parameter fails when layer attributes are customized (removed or reordered)
- GEOS-11606 geofence-server imports obsolete asm dep
- GEOS-11611 When Extracting the WFS Service Name from the HTTP Request A Slash Before the Question Marks Causes Issues
- GEOS-11630 REST API throws HTTP 500 When Security Metadata Has Null Attributes
- GEOS-11643 WCS input read limits can be fooled by geotiff reader
- GEOS-11647 Restore “quiet on not found” configuration for REST in global settings
- GEOS-11649 welcome page per-layer is not respecting global service enablement
- GEOS-11672 GWC virtual services available with empty contents
- GEOS-11681 MapML raster GetFeatureInfo not working
Task:
- GEOS-11608 Update Bouncy Castle Crypto package from bcprov-jdk15on:1.69 to bcprov-jdk18on:1.79
- GEOS-11631 Update MySQL driver to 9.1.0
- GEOS-11650 Update dependencies for monitoring-kafka module
- GEOS-11659 Apply Palantir Java format on GeoServer
- GEOS-11671 Upgrade H3 dependency to 3.7.3
- GEOS-11685 Bump jetty.version from 9.4.56.v20240826 to 9.4.57.v20241219
For the complete list see 2.26.2 release notes.
Community Updates
Community module development:
- GEOS-11635 Add support for opaque auth tokens in OpenID connect
- GEOS-11637 DGGS min/max resolution settings stop working after restart
- GEOS-11680 Azure COG assembly lacks mandatory libraries, won’t work
- GEOS-11686 Clickhouse DGGS stores cannot properly read dates
- GEOS-11687 OGC API packages contain gs-web-core
- GEOS-11691 Smart data loader accepts bigint and bigserial but not int8 postgresql type alias
Community modules are shared as source code to encourage collaboration. If a topic being explored is of interest to you, please contact the module developer to offer assistance.
About GeoServer 2.26 Series
Additional information on GeoServer 2.26 series:
Behind The Scenes
- GeoServer 3.0-RC, a crowdfunded success story
- GeoServer 3 First public release date
- GeoServer 3 Sprint Update
- GeoServer 2025 Q4 Developer Update
- GeoServer 3 Crowdfunding Goal Surpassed!
- GeoServer 2025 Q2 Developer Update
- GeoServer 3 Crowdfunding – Last Call!
- GeoServer 3 Crowdfunding Campaign Reaches Major Step: 80% Funding Completion
- GeoServer 2025 Roadmap
- GeoServer 2024 Q4 Developer Update
